How Managed Data Protection Solutions Can Protect Against Cyber Threats
How Managed Data Protection Solutions Can Protect Against Cyber Threats
Blog Article
How Managed Information Defense Safeguards Your Business From Cyber Hazards
In an age where cyber dangers are progressively sophisticated, the significance of handled data security can not be overemphasized. Organizations that carry out comprehensive safety procedures-- such as information security, accessibility controls, and continuous tracking-- are much better equipped to protect their sensitive information.

Recognizing Managed Data Protection
Managed data defense is an essential part of modern cybersecurity techniques, with about 60% of organizations opting for such solutions to protect their vital information possessions. This strategy involves outsourcing data defense obligations to specialized provider, allowing organizations to concentrate on their core service functions while guaranteeing durable safety procedures remain in location.
The essence of managed data defense hinges on its capacity to provide thorough options that include data back-up, recuperation, and hazard detection. By leveraging sophisticated technologies and expertise, took care of company (MSPs) can apply positive steps that mitigate dangers related to data violations, ransomware assaults, and various other cyber risks. Such solutions are created to be scalable, fitting the evolving demands of services as they adjust and expand to new difficulties.
Furthermore, managed information defense assists in compliance with governing needs, as MSPs commonly remain abreast of the current sector standards and practices (Managed Data Protection). This not only boosts the protection posture of a company yet additionally instills self-confidence among stakeholders relating to the honesty and confidentiality of their information. Ultimately, understanding handled information protection is essential for companies seeking to fortify their defenses against the ever-changing landscape of cyber hazards
Key Components of Information Protection
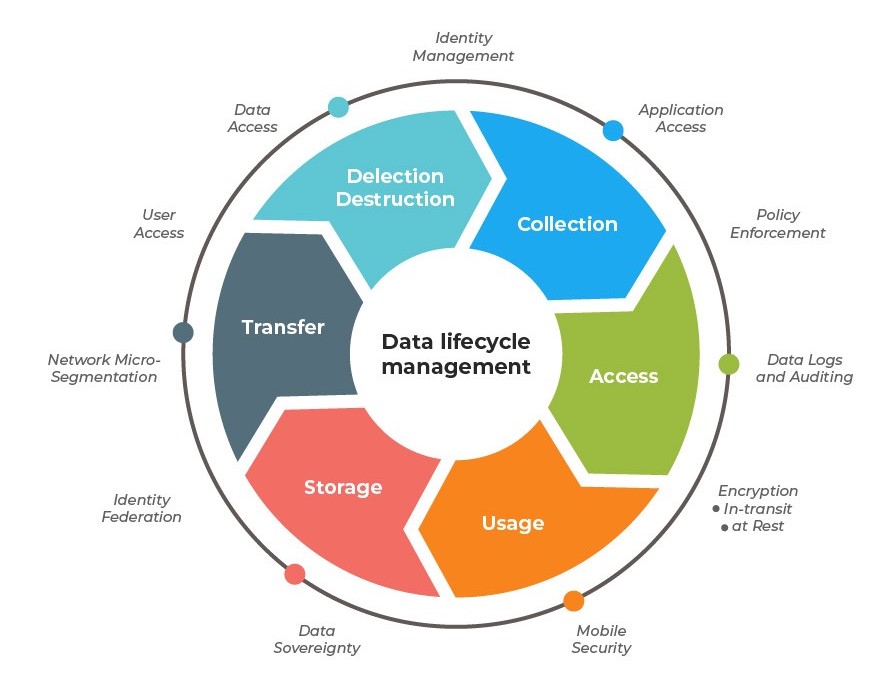
Effective information security strategies normally include several crucial parts that operate in tandem to safeguard delicate info. Data encryption is crucial; it changes readable information right into an unreadable style, making sure that even if unauthorized accessibility happens, the info continues to be protected.
Accessibility control is another crucial element, allowing companies to limit information accessibility to accredited employees just. This lessens the danger of inner breaches and improves liability. Normal information backups are crucial to guarantee that info can be brought back in the event of information loss or corruption, whether due to cyberattacks or unintended deletion.
Following, a robust safety and security policy need to be established to outline procedures for data taking care of, storage space, and sharing. This policy ought to be on a regular basis updated to adapt to advancing dangers. Furthermore, constant monitoring and auditing of data systems can detect anomalies and prospective violations in real-time, promoting swift responses to risks.
Advantages of Managed Services

Additionally, managed services assist in positive monitoring and hazard detection. MSPs use sophisticated innovations and devices to constantly keep track of systems, ensuring that anomalies are recognized and addressed prior to they escalate right into significant issues. This positive strategy not just minimizes response times but also mitigates the possible effect of cyber incidents.
Cost-effectiveness is an additional crucial advantage. By outsourcing data defense to an MSP, companies can avoid the considerable expenses related to in-house staffing, training, and technology investments. This allows firms to assign sources a lot more effectively while still taking advantage of top-tier security options.
Compliance and Regulatory Assurance
Ensuring conformity with sector guidelines and criteria is a critical element of information security that organizations can not forget. Regulative frameworks, such as GDPR, HIPAA, and PCI DSS, enforce strict requirements on just how companies manage and shield delicate information. Non-compliance can cause serious fines, reputational damages, and loss of customer trust fund.
Managed data security services assist companies navigate the facility landscape of conformity by visit here executing durable security actions tailored to meet details regulative demands. These services use organized techniques to data security, accessibility controls, and regular audits, ensuring that all procedures align with legal commitments. By leveraging these taken care of services, services can keep constant oversight of their information security methods, making sure that they adjust to evolving regulations.
In addition, detailed coverage and documentation supplied by managed data security services offer as valuable tools during conformity audits. These documents show adherence to established processes and standards, providing guarantee to stakeholders and regulative bodies. Ultimately, purchasing managed information protection not only fortifies an organization's cybersecurity posture but also infuses self-confidence that it is dedicated to preserving compliance and regulative guarantee in a progressively complex digital landscape.
Choosing the Right copyright
Choosing the ideal handled information protection copyright is critical for organizations aiming to enhance their cybersecurity structures. The primary step in this procedure is to examine the service provider's expertise and experience in the field of data protection. Seek a service provider with a tried and tested performance history of effectively protecting organizations versus numerous cyber threats, along with experience with industry-specific policies and conformity demands.
Furthermore, assess the range of services offered. An extensive copyright will deliver not only back-up and recovery services but also positive hazard detection, risk assessment, and case feedback capacities. It is vital to make certain that the service provider uses innovative innovations, consisting of security and multi-factor verification, to secure sensitive information.
Moreover, think about the degree of consumer support and solution degree arrangements (SLAs) supplied. Click Here A responsive assistance group can considerably impact your company's capacity to recover from events quickly. Lastly, evaluation endorsements and study from existing customers to determine fulfillment and reliability. By very carefully examining these variables, organizations can make an educated decision and pick a provider that lines up with their cybersecurity goals, ultimately reinforcing their protection versus cyber hazards.
Verdict
To conclude, managed data defense acts as an important defense against cyber threats by employing robust safety and security procedures, specific know-how, and advanced modern technologies. The combination of extensive techniques such as data encryption, access controls, and constant tracking not just mitigates threats yet additionally makes certain compliance with regulative standards. By outsourcing these solutions, companies can enhance their safety frameworks, helping with rapid recovery from data loss and cultivating self-confidence among stakeholders in the face of ever-evolving cyber dangers.
In an era where cyber risks are significantly advanced, the value of taken care of data security can not be overstated.The essence of managed data protection lies in its capability to use thorough solutions that consist of data back-up, recuperation, and danger discovery. Ultimately, recognizing taken care of data protection is important for organizations looking for to strengthen their defenses versus the ever-changing landscape of cyber risks.
In final thought, took care of information protection offers as an essential defense against cyber hazards by anchor employing robust safety steps, specialized know-how, and progressed innovations. Managed Data Protection.
Report this page